Introduction
In our everyday experience, physical objects follow strict and predictable rules. A ball thrown at a wall bounces back, and a car cannot cross a barrier without breaking through it. These observations form the foundation of classical physics, which governs the macroscopic world. Classical mechanics assumes that objects have definite positions, energies, and trajectories, and that motion is fully determined by forces and energy conservation.
However, when we move from the visible world to the microscopic realm of atoms, electrons, and subatomic particles, these familiar rules begin to fail. Nature behaves in ways that are often counter-intuitive and probabilistic rather than deterministic. One of the most fascinating phenomena arising from this quantum domain is quantum tunneling—a process in which particles pass through energy barriers that they seemingly should not be able to cross.
Quantum tunneling is not merely a theoretical curiosity. It is a fundamental mechanism behind nuclear fusion in stars, radioactive decay, modern electronic devices, and advanced scientific instruments. This phenomenon challenges classical intuition and reveals the true nature of reality at the smallest scales.
Understanding Quantum Tunneling
At its core, quantum tunneling refers to the phenomenon where a particle has a non-zero probability of passing through a potential energy barrier, even when its total energy is less than the height of that barrier.
In classical physics:i
- A particle approaching a barrier with insufficient energy must be reflected.
- The probability of crossing the barrier is strictly zero.
Quantum mechanics, however, introduces probability as a fundamental aspect of nature. According to this framework, particles are described by wavefunctions, mathematical entities that provide information about the likelihood of finding a particle at a particular position.
When a particle encounters a barrier:
- Its wavefunction does not abruptly end at the boundary.
- Instead, it penetrates into the barrier and decays exponentially.
- If the barrier is thin enough, the wavefunction may extend beyond it, allowing the particle to appear on the other side.
This process—where a particle effectively “passes through” a barrier without climbing over it—is known as quantum tunneling.
Wave–Particle Duality: The Foundation of Tunneling
Quantum tunneling is a direct consequence of wave–particle duality, one of the central principles of quantum mechanics. According to this principle:
- Every particle exhibits both particle-like and wave-like behavior.
- Electrons, protons, and even atoms can behave as waves under certain conditions.
Unlike classical particles, waves do not have sharply defined positions. They spread out over space, allowing parts of the wave to exist in regions that would be forbidden for a classical particle. When a quantum particle approaches a barrier, its wavefunction spreads into the barrier region, making tunneling possible.
This dual nature challenges our classical intuition but provides a more accurate description of the microscopic universe.
A Simple Analogy to Visualize Tunneling
To visualize quantum tunneling, imagine rolling a ball toward a hill.
- In classical physics, the ball must have enough energy to climb over the hill.
- If it lacks sufficient energy, it rolls back.
In quantum physics, the “ball” behaves like a wave:
- The wave spreads out as it approaches the hill.
- A portion of the wave may appear on the other side.
- When measured, the particle may be detected beyond the barrier.
The particle does not physically climb the hill—it tunnels through it.
Classical vs Quantum Mechanics
Classical View
According to classical mechanics, the kinetic energy of a particle is:
Since:
- Mass \(m\) is always positive
- Velocity squared \(v^2\) is always positive
Kinetic energy can never be negative. If a particle encounters a potential barrier of height \(V_0\) and its total energy \(E < V_0\), then its kinetic energy inside the barrier would be negative—an impossible situation in classical physics. Hence, total reflection is predicted.
Quantum Mechanical View
Quantum mechanics allows total reflection only when the barrier height is infinite. For a finite potential barrier, even if \(E < V_0\), there is a finite probability that the particle will appear on the other side.
This crucial difference gives rise to quantum tunneling.
Mathematical Perspective (Conceptual)
Quantum behavior is governed by the time-independent Schrödinger equation (TISE):
Here:
- \(\psi(x)\) is the wavefunction
- \(|\psi(x)|^2 \)represents probability density
- \(E\) is total energy
- \(V(x)\) is potential energy
The Schrödinger equation predicts that the wavefunction decays exponentially inside a barrier but does not become zero, allowing tunneling to occur.
Quantum Mechanical Tunneling: Potential Barrier Model
To understand tunneling rigorously, consider a one-dimensional finite potential barrier divided into three regions.
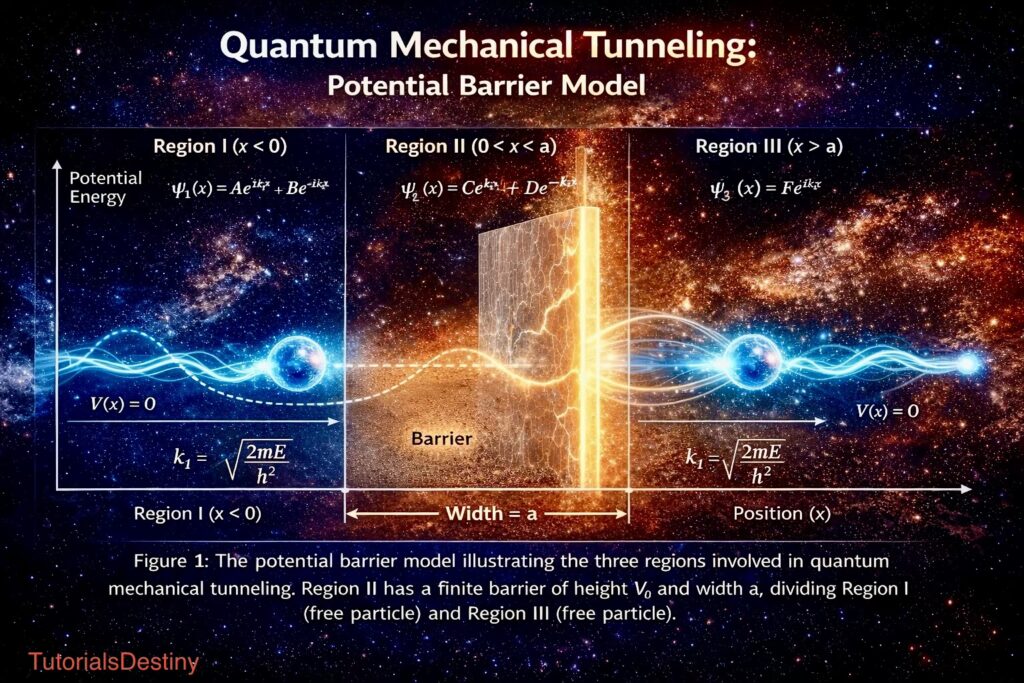
Potential Definition
\[V(x) = \begin{cases} 0, & x < 0 \quad \text{(Region I)} \\ V_0, & 0 \le x \le a \quad \text{(Region II)} \\ 0, & x > a \quad \text{(Region III)} \end{cases}\]
where:
- \(V_0\) is the barrier height
- \(a\) is the barrier width
- \(E < V_0\)
Region I: \( x < 0\) (Incident and Reflected Waves)
The Schrödinger equation becomes:
\[\frac{d^2 \psi}{dx^2} + k_1^2 \psi = 0\]
where:
\[k_1 = \sqrt{\frac{2mE}{\hbar^2}}\]
The solution is:
\[\psi_1(x) = A e^{ik_1 x} + B e^{-ik_1 x}\]
- First term: incident wave
- Second term: reflected wave
Region II: \(0 < x < a\) (Inside the Barrier)
Here, \(E < V_0\), so the equation becomes:
\[\frac{d^2 \psi}{dx^2} – k_2^2 \psi = 0\]
with:
\[k_2 = \sqrt{\frac{2m(V_0 – E)}{\hbar^2}}\]
The solution is:
\[\psi_2(x) = C e^{k_2 x} + D e^{-k_2 x}\]
This region features exponentially decaying wavefunctions, representing barrier penetration.
Region III: \( x > a\) (Transmitted Wave)
The equation again becomes:
\[\frac{d^2 \psi}{dx^2} + k_1^2 \psi = 0\]
The solution is:
\[\psi_3(x) = F e^{ik_1 x}\]
Only a transmitted wave exists here; no wave travels backward.
Transmission and Reflection Coefficients
Applying boundary conditions at \(x = 0\) and \(x = a\), the transmission coefficient is obtained as:
\[T = \frac{1}{1 + \frac{V_0^2}{4E(V_0 – E)} \sinh^2(k_2 a)}\]
This expression shows that:
- \(T \neq 0\) even when \(E < V_0\)
- Tunneling probability decreases with increasing barrier width and height
- Lighter particles tunnel more easily
Quantum Tunneling in Nature
1. Nuclear Fusion in the Sun
Quantum tunneling is essential for the energy production in stars. Inside the Sun:
- Protons repel each other due to electrostatic forces.
- Classically, their thermal energy is insufficient to overcome this repulsion.
- Quantum tunneling allows protons to approach closely enough for the strong nuclear force to bind them.
This process enables nuclear fusion, releasing vast amounts of energy that power the Sun and sustain life on Earth. Without quantum tunneling, stars would not shine.
2. Radioactive Alpha Decay
In radioactive nuclei:
- Alpha particles are trapped inside the nucleus by a strong potential barrier.
- Classical physics predicts they should remain confined indefinitely.
- Quantum tunneling allows them to escape.
This escape results in alpha decay, a fundamental form of radioactivity. The rate of decay depends on the tunneling probability, which explains why different radioactive elements have different half-lives.
Technological Applications of Quantum Tunneling
1. Scanning Tunneling Microscope (STM)
The scanning tunneling microscope is one of the most direct technological applications of quantum tunneling. It operates by:
- Bringing a sharp metallic tip extremely close to a surface.
- Applying a small voltage between the tip and the surface.
- Measuring the tunneling current produced by electrons.
This current is highly sensitive to distance, allowing scientists to image individual atoms. The STM revolutionized surface science and nanotechnology.
2. Semiconductor Devices
Quantum tunneling plays a crucial role in modern electronics, especially as devices shrink to nanometer scales.
Applications include:
- Tunnel diodes
- Flash memory
- Transistors in integrated circuits
As components become smaller, tunneling effects become unavoidable. Engineers must carefully design devices to either utilize or suppress tunneling, depending on the application.
3. Quantum Computing
In quantum computing:
- Tunneling enables particles to transition between quantum states.
- It plays a role in quantum annealing and optimization algorithms.
Quantum tunneling allows quantum computers to explore solution spaces more efficiently than classical computers for certain problems.
Importance of Quantum Tunneling
Quantum tunneling is not merely a theoretical concept. Its importance lies in its ability to:
- Explain phenomena that classical physics cannot
- Enable advanced experimental techniques
- Drive technological innovation
- Deepen our understanding of the quantum nature of reality
It demonstrates that probability, rather than certainty, governs the microscopic world.
Limitations and Common Misconceptions
Despite its extraordinary nature, quantum tunneling has clear limitations:
- It does not allow macroscopic objects to pass through walls.
- The tunneling probability for large objects is effectively zero.
- It does not violate conservation of energy or physical laws.
Quantum tunneling is significant only at atomic and subatomic scales.
Philosophical Implications
Quantum tunneling raises profound philosophical questions about determinism and reality. It suggests that:
- Nature is fundamentally probabilistic.
- Events are governed by likelihood rather than certainty.
- Observation plays a critical role in determining outcomes.
These ideas challenge classical notions of causality and determinism.
Conclusion
Quantum tunneling stands as one of the most striking and beautiful phenomena in physics. It reveals a universe where particles behave as waves, barriers are not absolute, and the impossible becomes possible—at least with some probability. From powering the stars to enabling cutting-edge technology, quantum tunneling silently shapes both the cosmos and our everyday lives.
By challenging our intuition and expanding our understanding of nature, quantum tunneling reminds us that reality at its deepest level is far richer and stranger than it appears.
In the quantum world, even the gimpossible has a chance.